Connecting to a public network is a gamble with your data. Most people see free guest Wi-Fi as a convenience, but from a technical standpoint, it is a way for others to monitor your traffic. When you use these networks, you are trusting a third party to secure a connection that is often left intentionally wide open.
Accucom Blog
Imagine if a master locksmith suddenly announced that the standard deadbolt—the exact one installed on almost every office door in the country—had a hidden flaw. Worse, imagine they just proved exactly how to pick it. You wouldn't just sit there and hope for the best. You'd be calling a professional to get new, secure locks installed immediately.
I’ve spent my entire career telling people that technology is a tool to help you do more. Unfortunately, the bad guys have been using that same tool to build something truly unsettling: the deepfake.
We’ve officially entered an era where you can't necessarily trust your eyes or ears during a business call. It isn’t just for making funny movie parodies anymore; it’s being weaponized to bypass your security and drain your bank accounts.
Most business owners I meet have a backup plan. In the worst situation, it's a lone external drive humming in the corner or a basic cloud sync. While these are good first steps, they often harbor a hidden danger: a single point of failure. If your office faces a fire, that external drive is toast. If a staff member accidentally wipes a folder and it instantly syncs to the cloud, your data could vanish before you even realize it's gone. To build a strategy you can actually sleep on, we use the 3-2-1-1 Rule.
The biggest security risks to your business often come from within your own office. This doesn’t mean your employees are criminals; in fact, the problem usually starts because your staff is hardworking and helpful.
When people are determined to do a great job, they often develop habits that unintentionally put your data at risk. Here is how that happens and what you can do to fix it.
Does your leadership team follow the same security rules as everyone else, or are there special exceptions made for the executive suite? One of the most dangerous vulnerabilities in a business is the CEO who’s too busy to adhere to the multi-factor authentication policy or who insists on having administrative access to every file in the company. This is precisely why cybercriminals target high-level executives; the likelihood that they have access to data they shouldn’t is much higher than the average employee.
Towards the end of February of this year, LexisNexis Legal & Professional fell victim to a data breach in which the responsible party accessed the data analytics company’s Amazon Web Services infrastructure due to an unpatched application. While the data leak itself was (according to LexisNexis L&P, at least) relatively minimal, this breach presents an opportunity to reiterate the importance of an easy-to-overlook vulnerability that quietly causes problems for businesses of all sizes.
There’s no denying the convenience that so many of technology's essential features and functions can now be managed with a simple command, if not completely automated, thanks to the Internet of Things. With the IoT, everything is augmented by a miniature computer… but these devices are built to be convenient and (for lack of a better term) cheap.
As such, you could potentially have numerous backdoors into your business network.
Are you still depending on your business being so small that it flies “under the radar” of potential threats? The most dangerous mindset you can have is that you’re too small for a hacker to care about your data. In reality, hackers don’t care how big your business is; they care about what data they can steal, and there’s plenty of it on your infrastructure.
If you’re counting on a big, dramatic hacking attack being the method of choice for any cybercriminal with you in their sights, I have some bad news.
In reality, cybercrime is sneaky. A threat quietly infiltrates your network, lying in wait and biding its time, gradually collecting data until the perfect moment arrives. On average, a hacker spends 180 days in this reconnaissance mode. You need to know the warning signs that something isn’t quite right.
You know your business needs multi-factor authentication, but chances are you see a lot of pushback from your employees because of how inconvenient it is for their work. In an effort to please everyone, you implement SMS authentication out of sheer convenience, but the innovation of SIM swapping means that this method of MFA is a vulnerability rather than a security solution. A hacker doesn’t need to steal your phone; they just need to trick a customer service representative at your mobile carrier to port your phone number to a new SIM card they control. If your second factor can be stolen so easily, what’s your business supposed to do?
It’s known that baby toys can aid in all manner of developmental processes, so take a moment to imagine what the future of technology holds for toys. Will they continue in the same vein as toys that teach color recognition, teamwork, sharing, and creativity, or will they get even more wild and out of the box? Regardless, one thing is for certain: security challenges exist just on the horizon and will have to be addressed if parents want to keep their children safe.
By now, AI isn’t just a buzzword in the 2026 boardroom—it’s the plumbing. But as developers race to push the tech into uncharted territory, the line between "breakthrough" and "breakdown" has become razor-thin. Today’s story is a cautionary tale about the leap from AI that talks to AI that acts, and how a single developer’s viral hit accidentally birthed a multi-million dollar heist and a digital cult.
The most sophisticated firewall in the world cannot stop a human being from making a split-second mistake. Cybercriminals are not just hacking code; they are hacking your employees. By exploiting high-stress environments and the natural desire to be helpful, hackers create click-first, ask-later scenarios that can bypass your entire security stack in an instant.
To defend your business, you do not necessarily need a bigger budget, while that would be nice. You need a better habit. Enter the 3-Second Rule.
If you asked your team what they remember from the last annual security compliance video, we bet they’d be hard-pressed to remember anything of importance. That’s because most small business security training is like going to the dentist; you go once a year, and only because you have to. The unfortunate reality is that most people are going about security training from the “annual compliance” perspective, which isn’t doing your business any favors, and more importantly, doesn’t change their behavior.
Traditional cybersecurity has long been built on a foundation of restriction and reprimand. However, treating employees as the weakest link creates a dangerous paradox: the more you monitor and scold your team, the higher your actual risk becomes.
When an employee fears professional retaliation for a digital mistake, they don't become more careful… they become more secretive. They delete the suspicious email, close the flickering tab, and pray. This silence is a gift to threat actors, giving them the weeks or months they need to move through your network undetected.
We’ve all seen the Internet represented as an iceberg in images and videos explaining the deep web. The surface web—the part you use every day—is just the tip. Below that is the Deep Web (password-protected sites), and at the very bottom is the Dark Web, a hidden layer where anonymity is the primary currency. From a business perspective, the Dark Web isn’t just a scary place; it is a thriving marketplace for your company’s stolen assets.
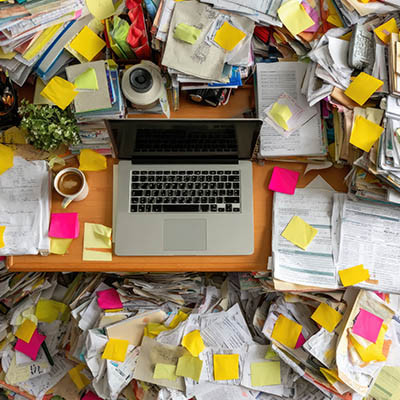
Clutter is a part of life, but one place you absolutely don’t want it is your business’ network. This clutter is called “digital cruft,” which 1) is an actual word, and 2) creates serious problems if you let it accumulate. Your digital cruft can lead to significant vulnerabilities that put your network at risk.
As a cybersecurity professional, I've seen organizations of all sizes and sectors make a critical, often fatal, mistake: they wait for the water to boil. They operate under a reactive cybersecurity model, adopting the same slow, passive approach as the hapless subject of the boiled frog analogy.
It’s a tale I recently rediscovered, and it's a chillingly perfect metaphor for modern cyberrisk. Imagine a frog enjoying a cool bath as the water is slowly, almost imperceptibly, heated. It thinks it’s enjoying a relaxing bath until the water reaches a lethal temperature. By then, it’s too late. The danger has crept up, and the frog is boiled.